Configure GlobalSearch for Provider Authentication
To enable the Provider Authentication option, the GlobalSearch administrator will need to configure your chosen provider on the Server. Update config.json in your GlobalSearch website's Square9Web folder with the provider specific settings. Your administrator will need to provision the application in the provider before performing the configuration outlined below.
Okta
The Okta administrator will need to provide the Okta Client ID and Okta Domain to add into GlobalSearch's config.json. GlobalSearch Cloud customers can provide these values to support and they will be provisioned on your behalf.
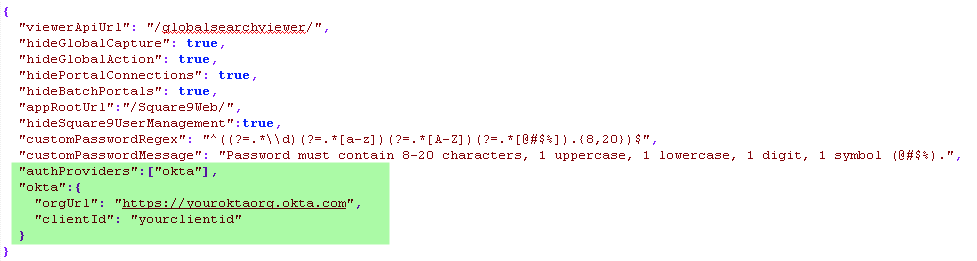
The authProviders key and the okta key and object are required. Be sure to update the values with settings specific to your Okta Application.
API Access
Customers who do not license API Access Management in Okta MUST follow additional provisioning steps outlined below. You will most commonly see a message indicating “Feature Not Licensed” after a user authenticates in the Okta challenge window.
Customer who do not leverage API Access Management will need an additional parameter in the okta object of the config.json. When adding another line, do not forget to add a comma after the clientId.
"endpoint": "/oauth2/v1/authorize"Next, the Square9API web.config needs additional appSettings entires.
<add key="urn:square9:webauthentication:okta:clientid" value="CLIENT-ID-FROM-OKTA-APP-HERE" />
<add key="urn:square9:webauthentication:okta:clientsecret" value="CLIENT-SECRET-FROM-OKTA-APP-HERE" />Be sure to replace your Client ID and Client Secret values for successful operation.
Login Page
Once provisioned, Provider Authentication will add a “Login with” option to the login page.
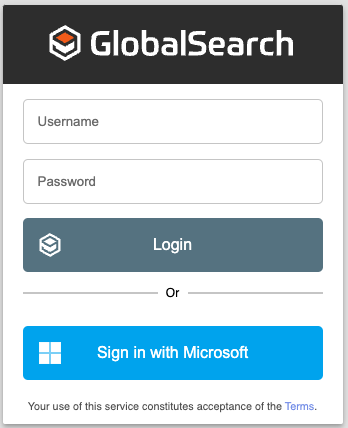
Common Login Dialog For Square 9 Apps
Customers can hide the Username and Password for Square 9 logins if desired. Simply add a new entry to the config.json noted above:
"hideBasicLogin":true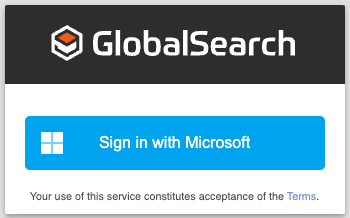
Login Dialog With Basic Login Hidden
User will still have the opportunity to provide Square 9 credentials when appropriate. This is common for Admin level users, or for users that might be provisioned outside of your organization. Simply double click the GlobalSearch logo to expose the Username and Password options.